At Wasp, we’re engaged on a config language / DSL for constructing internet apps that integrates with React & Node.js.
This requires us to deeply perceive totally different components of what constitutes an online app, so as to have the ability to mannequin them in our DSL.
Lately our focus was on entry management, and I made a decision to seize the learnings on this weblog publish, to assist others shortly stand up to hurry on how you can do entry management in internet apps.
So, if you’re new to entry management in internet apps, or have been doing it for a while however wish to get a greater thought of normal practices, learn alongside!
Fast overview of what this weblog publish covers:
- Permissions, yay! Wait, what are they although? (fast overview of primary phrases)
- The place will we test permissions in an online app: frontend vs backend vs db
- Widespread approaches (RBAC, ABAC, …)
- OWASP suggestions
- Implementing entry management in apply
- Abstract
1. Permissions, yay! Wait, what are they although?
Except your internet app is usually about static content material or is a type of artwork, it should probably have a notion of customers and consumer accounts.
In such a case, you will want to know which consumer has permissions to do what -> who can entry which assets, and who can execute which operations.
Some widespread examples of permissions in motion:
- Person can entry solely their very own consumer account.
- If the consumer is an admin, they will ban different customers’ accounts.
- Person can learn different customers’ articles, however cannot modify them.
- The title and outline of the article behind the paywall are publicly accessible, however the content material will not be.
- Person can ship an electronic mail invitation to as much as 10 future customers per day.
Aha, you imply entry management! Sorry, authorization! Hmm, authentication?
There are totally different phrases on the market (authentication, authorization, entry management, permissions) which might be typically confused for one another, so let’s shortly make clear what every one in every of them stands for.
1) Authentication (or as cool children would say: authN)
Act of verifying the consumer’s identification.
Solutions the query “Who’re they?“
A: Knock Knock
B: Who’s it?
A: Person!
B: Person who?
A: Authorization: Primary myusername:mypassword
-> sure, you seen accurately, that is an instance of widespread authentication technique however HTTP header known as “Authorization”! Bizarre! However it all is sensible when you squint exhausting sufficient: (https://stackoverflow.com/questions/30062024/why-is-the-http-header-for-authentication-called-authorization).
2) Authorization (or as cool children would say: authZ)
Strategy of figuring out entry rights that consumer has.
Solutions the query “Are they allowed to do that?“
Usually you want the consumer to be authenticated at this level already, so you will have details about them based mostly on which you’ll determine if they’re allowed to do one thing.
3) Entry Management
A better-level time period (in comparison with authN and authZ) that encompasses the entire means of guaranteeing that solely allowed events can entry particular assets (controlling entry to assets -> entry management).
Usually consists of authentication and/or authorization as its steps.
Additionally typically used within the wild interchangeably with simply “authorization”.
Reference (OWASP): https://www.cgisecurity.com/owasp/html/ch08.html
4) Permission(s)
A extra normal/casual time period, closest in that means to “authorization” when used within the context of pc science.
Permission to entry a useful resource known as authorization.
All collectively
Let’s see these phrases utilized in a sentence by observing the next imagined pull request (PR):
Title: Added entry management to the app.
Description:
I carried out a method for customers to authenticate by way of electronic mail and password or by way of Google.
On the server-side, I added permission checks to most of our REST API handlers, to make sure an authenticated consumer is licensed to execute them.
If the consumer will not be licensed, we throw an HTTP error 403.
There are additionally some public components of REST API the place the consumer doesn’t should be authenticated.
2. The place will we test permissions in an online app: frontend vs backend vs database
We defined a bunch of phrases, let’s have a look at now how entry permission checks are literally achieved in apply!
In a typical internet app, you’ll have a frontend, backend (server), and database.
The frontend will probably be issuing instructions to the server, which then executes operations and presumably modifies the database (on their behalf). Since customers don’t have direct entry to the database, and because the frontend is inherently not safe, that leaves the server because the central place the place all of the essential entry management must occur.
Frontend (browser)
By frontend we imply internet consumer -> code (e.g. JS) that executes within the browser.
The frontend is right here to assist customers situation instructions in direction of the server by way of which customers can entry and/or modify the assets of our internet app (that are most frequently saved within the database).
Since customers can manipulate the frontend code as they need, we will not actually do any permissions checks within the frontend code, we will not belief it!
Any permission checks we do on the frontend, we might want to repeat on the server in any case.
If that is the case, ought to we in any respect test permissions on the frontend, and what’s the goal of that?
The principle motive for doing any permissions checks on the frontend is ergonomics/consumer expertise -> by having UI focus solely on assets they will change, we make it simpler for customers to grasp what they will do in our internet app and ensure they do not waste time on making an attempt to explain complicated operations that server will then not be capable of execute.
So, for instance, our frontend code can conceal/omit sure fields within the UI kind if the consumer should not be capable of entry them, it may stop opening sure pages, or conceal/omit sure buttons in the event that they set off operations that the consumer will not be allowed to carry out.
Takeaway: Permission checks on frontend aren’t there for safety, however just for ergonomics / enhancing consumer expertise.
Backend (server)
The server is a vital place to implement entry management. It exposes an API that the frontend (browser) and/or different companies devour. Whereas doing that, they authenticate with the server, in order that server is aware of who they’re, after which they ask (i.e. by way of REST API or GraphQL API) the server to execute sure operations (i.e. creating, updating, or fetching one thing). It’s the server’s job to determine if they’re allowed (licensed) to carry out these operations (on specified assets / with supplied arguments) and to reject them if they aren’t.
At its core, permissions checks on the server are right here to test for every API endpoint if the caller is allowed to execute it. Usually they’re executed on the very begin of the API endpoint logic, however typically they’re additionally intertwined with the remainder of the endpoint handler logic.
Moreover defining checks at API/operation stage, they’re additionally typically outlined on the information/mannequin stage. Which means that they’re tied to particular information fashions (usually from the database), as a part of information entry logic (ORM), and are defining who can entry particular area(s), and even the entire information mannequin.
Instance of attaching permission checks to the info mannequin instantly within the GraphQL schema (from this blog post):
For a extra subtle RBAC method, with an extra layer of indirection (permissions), learn on.
Database
Normally, customers don’t have direct entry to the database in any respect, as an alternative, they have an effect on it by way of the server. In such a case, there isn’t a must do particular database entry management moreover regular constraints that you’ll have in your DB to make sure information mannequin integrity, like uniqueness, validations, and related. That mentioned, in some conditions, you may wish to do it, however we won’t get into that on this article.
3. Widespread approaches (RBAC, ABAC, …)
The commonest approaches to entry management are RBAC (Position-Primarily based Entry Management) and ABAC (Attribute-Primarily based Entry Management), with RBAC having the robust lead (however ABAC is choosing up).
Though much less widespread, we may even shortly point out ReBAC as an “in-between” possibility.
RBAC – Position-based entry management
Roles rule :D! In RBAC, roles are the central idea. Some instance roles could be admin, visitor, author, moderator, …. When figuring out if a sure consumer has entry, we test their roles and decide their entry rights based mostly on it. For instance, admin can delete different customers, articles, and tasks, however visitor can’t modify any assets, solely learn articles.
Professional recommendation (thanks Karan!): Whereas we might be checking the consumer’s roles instantly within the permission checks, it’s even higher (and really helpful by OWASP) so as to add a layer of indirection → permissions. So roles are connected to customers, permissions are connected to roles, and permission checks test permissions (who would count on that :)!?).
For instance, a consumer may need position admin, and position admin has permissions updateArticle and deleteArticle connected to it. Then, when figuring out if a consumer can delete the article, we first fetch his position, then we fetch the permissions connected to that position, and at last test if deleteArticle is current amongst these → in that case, they will proceed with the deletion!
This manner, if we determine a sure position ought to have extra or fewer permissions, we simply add or take away the permission in query to the position, and that’s it! We don’t should undergo each permission test and replace its logic (which we must do if we have been checking instantly in opposition to roles).
RBAC is widespread as a result of it’s comparatively easy and it displays the fundamental enterprise area fairly properly – typically we’re considering within the phrases of roles in the true world, so it’s simple to know and perceive. There are many options and frameworks on the market that implement RBAC.
Whereas a superb match for a lot of widespread use instances, there’s a downside to RBAC – when entry management turns into complicated (which often occurs as the net app evolves and grows huge), RBAC typically fails in providing wanted granularity in a sublime method, leading to unwieldy and overly-complex entry management logic.
ABAC – Attribute-based entry management
In ABAC, key thought is that you simply outline a bunch of entry management guidelines the place every rule takes totally different “attributes” as enter. When it’s essential to test if a consumer is allowed to do smth, you run the foundations and if all the foundations go, it’s a go, but when a single rule fails, it’s a no go.
Rule attributes will be something, however often, they fall into 4 classes:
- Topic: details about a consumer (i.e. consumer’s id or title)
- Motion: operation they wish to carry out (i.e. studying an Article)
- Object: assets they wish to function on (i.e. an Article),
- Surroundings/context: i.e. present time of the day or variety of earlier requests that the consumer did within the final hour.
Let’s observe the instance from earlier than the place we needed to know if consumer is allowed to delete an article.
In ABAC, we may outline an motion “deleteArticle”, after which outline a rule that takes consumer(topic), motion, object, and extra context. That rule would test if motion is “deleteArticle” → in that case, it will consider if consumer is allowed to delete the article specified as an object, by checking some properties of consumer, perhaps even position, or by checking if consumer is proprietor of that article.
Then, when consumer really points a command to delete an article, we’d ask our entry management system to run it in opposition to all the foundations it has, whereas giving it the (consumer, “deleteArticle”, article, context) tuple → many of the guidelines would say all is okay since they aren’t involved with “deleteArticle” motion, however the ones which might be (just like the one we outlined above) should all go with a view to really permit the entry.
ABAC may be very versatile and normal as an method, and you could possibly simply implement RBAC (and plenty of different approaches) in ABAC (by checking the consumer’s position as one of many attributes) → due to this fact it’s extra normal/expressive than RBAC.
Nonetheless, ABAC is extra complicated to implement, and it’s also dearer performance-wise, resulting from needing to test a number of guidelines every time that entry management test is being carried out.
ReBAC – Relationship-based entry management
Roles (RBAC) will be missing when it’s essential to grant entry based mostly on relationship-related questions like “is that this consumer proprietor of this text” or “does this consumer belong to this workspace”.
Whereas ABAC can simply deal with this, you could possibly additionally contemplate it a bit too highly effective if all it’s essential to describe are relationships → and that is the place ReBAC is available in.
Whereas there are other ways one may go about implementing ReBAC, the only one is to construct on high of RBAC by introducing an idea of “relationship” guidelines to your entry management logic after which checking these alongside the roles. So RBAC with a touch of ABAC (centered on relationships).
4. OWASP suggestions
When trying on-line for “official”/standardized suggestions on how you can do entry management in internet apps, you’ll most probably discover assets produced by OWASP.
Definition of OWASP: The Open Net Utility Safety Mission® (OWASP) is a nonprofit basis that works to enhance the safety of software program.
I discovered that they’ve fairly just a few assets on how you can do entry management in internet apps, essentially the most fascinating being the next:
From their supplies I extracted a few details that made essentially the most sense to me:
- Centralize the entry management logic so it’s simple to assessment.
- Deny entry by default.
- Choose ABAC over RBAC.
5. Implementing entry management in apply
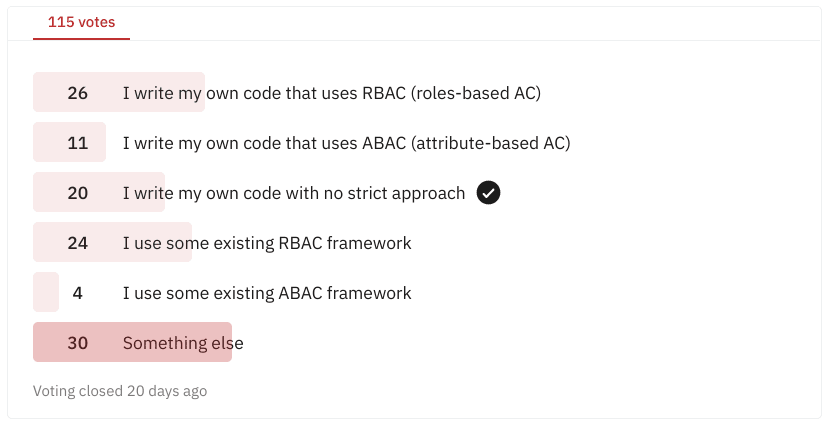
Right here’s a Reddit poll I did on r/webdev.
An fascinating discovering is that despite the fact that the pattern is fairly small, it’s clear that devs choose RBAC over OWASP-recommended ABAC.
I imagine this is because of 2 foremost causes: RBAC is easier + there are extra libraries/frameworks on the market supporting RBAC than ABAC (once more, resulting from it being less complicated).
It does appear that ABAC is choosing up just lately although, so it will be fascinating to repeat this ballot sooner or later and see what modifications.
Natural improvement
Usually, we add permission checks to our internet app one after the other, as wanted. For instance, if we’re utilizing NodeJS with ExpressJS for our server and writing middleware that handles HTTP API requests, we’ll add a little bit of logic into that middleware that does some checks to make sure a consumer can really carry out that motion. Or perhaps we’ll embed “checks” into our database queries in order that we question solely what the consumer is allowed to entry. Usually a mix.
What will be harmful with such an natural method is the complexity that arises because the codebase grows – if we don’t put sufficient effort into centralizing and structuring our entry management logic, it may develop into very exhausting to motive about it and to do constant updates to it, resulting in errors and vulnerabilities.
Think about having to switch the net app in order that consumer can now solely learn their very own articles and articles of their associates, whereas earlier than they have been allowed to learn any article. If there is just one place the place we are able to make this replace, we may have a pleasant time, but when there are a bunch of locations and we have to hunt these down first after which ensure that they’re all up to date in the identical method, we’re in for lots of bother and lot of house to make errors.
Utilizing an current answer
As an alternative of determining on our personal how you can construction the entry management code, typically it’s a better option to make use of an current entry management answer! Moreover not having to determine and implement every little thing by yourself, one other huge benefit is that these options are battle-tested, which is essential for the code coping with the safety of your internet app.
We are able to roughly divide these options into frameworks and (exterior) suppliers, the place frameworks are embedded into your internet app and shipped along with it, whereas suppliers are externally hosted and often paid companies.
A few widespread options:
-
https://casbin.org/ (a number of approaches, a number of languages, supplier)
- Open supply authZ library that has help for a lot of entry management fashions (ACL, RBAC, ABAC, …) and plenty of languages (Go, Java, Node.js, JS, Rust, …). Whereas considerably complicated, it’s also highly effective and versatile. In addition they have their Casdoor platform, which is authN and authZ supplier.
-
https://casl.js.org/v5/en/ (ABAC, Javascript)
- Open supply JS/TS library for ABAC. CASL offers you a pleasant approach to outline the ABAC guidelines in your internet / NodeJS code, after which additionally test them and name them. It has a bunch of integrations with widespread options like React, Angular, Prisma, Mongoose, … .
-
https://github.com/CanCanCommunity/cancancan (Ruby on Rails ABAC)
- Identical like casl.js, however for Ruby on Rails! Casl.js was really impressed and modeled by cancancan.
-
https://github.com/varvet/pundit
- Standard open-source Ruby library centered across the notion of insurance policies, supplying you with the liberty to implement your individual method based mostly on that.
-
https://spring.io/projects/spring-security
- Open supply authN and authZ framework for Spring (Java).
-
https://github.com/dfunckt/django-rules
- A generic, approachable open supply framework for constructing rule-based methods in Django (Python).
-
Auth0 (supplier)
- Auth0 has been round for a while and might be the preferred authN supplier on the market. Whereas authN is their foremost providing (they offer you SDKs for authentication + they retailer consumer profiles and allow you to handle them by their SaaS), additionally they assist you to outline authZ to some extent, by way of RBAC and insurance policies.
-
https://www.osohq.com/ (supplier, DSL)
- OSO is an authZ supplier, distinctive in a method that they’ve a specialised language for authorization (DSL, referred to as Polar) by which you outline your authorization guidelines. They arrive with help for widespread approaches (e.g. RBAC, ABAC, ReBAC) but additionally help customized ones. Then, you should utilize their open supply library embedded in your utility, or use their managed cloud providing.
-
https://warrant.dev/ (Supplier)
- Comparatively new authZ supplier, they’ve a dashboard the place you’ll be able to handle your guidelines in a central location after which use them from a number of languages by way of their SDKs, even on the consumer to carry out UI checks. Guidelines may also be managed programmatically by way of SDK.
-
https://authzed.com/ (Supplier)
- AuthZed brings a specialised SpiceDB permissions database which they use as a centralized place for storing and managing guidelines. Then, you should utilize their SDKs to question, retailer, and validate utility permissions.
Abstract (TLDR)
- Authentication (authN) solutions “who’re they”, authorization (authZ) solutions “are they allowed to”, whereas entry management is the overarching time period for the entire means of performing authN and authZ.
- Doing entry management on the frontend is only for present (for enhancing UX) and you may’t depend on it. Any and all actual entry management must be achieved on the server (presumably a bit within the db, however usually not wanted).
- Whereas it’s okay to start out with a easy entry management method firstly, you have to be prepared to change to a extra superior method as soon as the complexity grows. The preferred approaches for doing entry management are RBAC (role-based) and ABAC (attribute-based). RBAC is less complicated to get going with, however ABAC is extra highly effective.
- It’s best to ensure that your entry management has as little duplication as doable and is centralized, with a view to cut back the prospect of introducing bugs.
- It’s often good to use current options, like entry management frameworks or exterior suppliers.
Entry management in Wasp
In Wasp, we don’t but have particular help for entry management, though we’re planning so as to add it sooner or later. Because it appears in the meanwhile, we’ll most likely go for ABAC, and we might love to supply a approach to outline entry guidelines each on the Operations stage and at Entity (information mannequin) stage. Resulting from Wasp’s mission to supply a extremely built-in full-stack expertise, we’re excited in regards to the prospects this presents to supply an entry management answer that’s built-in tightly with the entire internet app, by the entire stack!
You may try our dialogue about this in our “Support for Permissions” RFC.
Because of the reviewers
Karan Kajla (professional recommendation on RBAC!), Graham Neray (nice normal recommendation + identified ReBAC), Dennis Walsh (superior recommendations how you can have article learn higher), Shayne Czyzewski, Matija Sosic, thanks for taking the time to assessment this text and make it higher! Your recommendations, corrections, and concepts have been invaluable.